
10 Things You Should Do to Ensure Physical Cybersecurity
Its not just Santa coming through your chimney this holiday season If youre not careful unwanted guests may look to enter as well taking physical...
Explore related posts tagged with "cloud cybersecurity"

Its not just Santa coming through your chimney this holiday season If youre not careful unwanted guests may look to enter as well taking physical...

IT security is a game of cat and mouse Bad actors are continuously developing new methods for disrupting systems and CTOs CIOs and their teams are ...

WHAT IS A BREAK GLASS PROCEDUREYouve probably spotted breakglass points or boxes in a building Usually smashing the glass allows quick acc...

Every organization has data and cyber security policies This is a nonnegotiable protection that companies rely on to maintain privacy over intellect...
Dont be afraid of cyber security The number of breaches and hacks in 2018 might seem scary but security tools are advancing almost as quickly as th...

Moving your data and applications to the cloud is one thing Maintaining compliance too is something else altogether and many SMBs and organizations ...
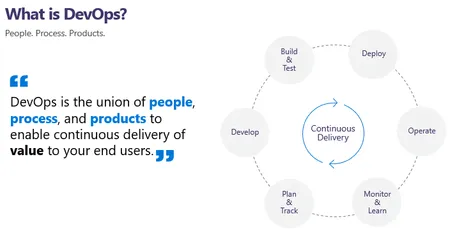
Using Azure DevOps for IT Management - Leverage Azure DevOps for effective IT management, automating processes for building, continuous testing, and deployment, even if you're not part of a software development team....

Businesses that deal in healthcare know the importance of HIPAA and HITECH compliance Violations of the privacy and security rules can result in larg...

Phishing attacks are the most common method of credential theft, with a low barrier to entry (You don't need to know much more than how to make a web page and write an email) and ever increasing sophistication. This morning, one of our ...

As explored in detail in Part 1 of this Zero Trust Security series the standard castle-and-moat, perimeter-styled network defense has been rendered practically useless in this new era of cloud computing, mobile devices, IoT, and other technologies...