Securing the Remote Workforce
In todays professional environment its never been more important to have a secure remote workforce There was a time when working remotely remained...

In today’s professional environment, it’s never been more important to have a secure remote workforce. There was a time when working remotely remained a privilege, not a right. With the onset of COVID-19 and the rapid response posture it’s forced so many companies to adopt in the past few weeks, those days are long gone.
For the foreseeable future, remote work is decidedly the new normal. This can be a transition for some companies. While your employees have the same functional capabilities they have in a traditional office, not having them in the same physical space can lead to some communication issues for teams that aren’t as well-versed in remote work.
It’s on the company’s leadership to ensure no glaring vulnerabilities emerge as a result of this shift. One area in which companies will need to be extra vigilant is with their cybersecurity. Let’s take a closer look at the approach you should take with your remote teams to build a secure remote workforce.
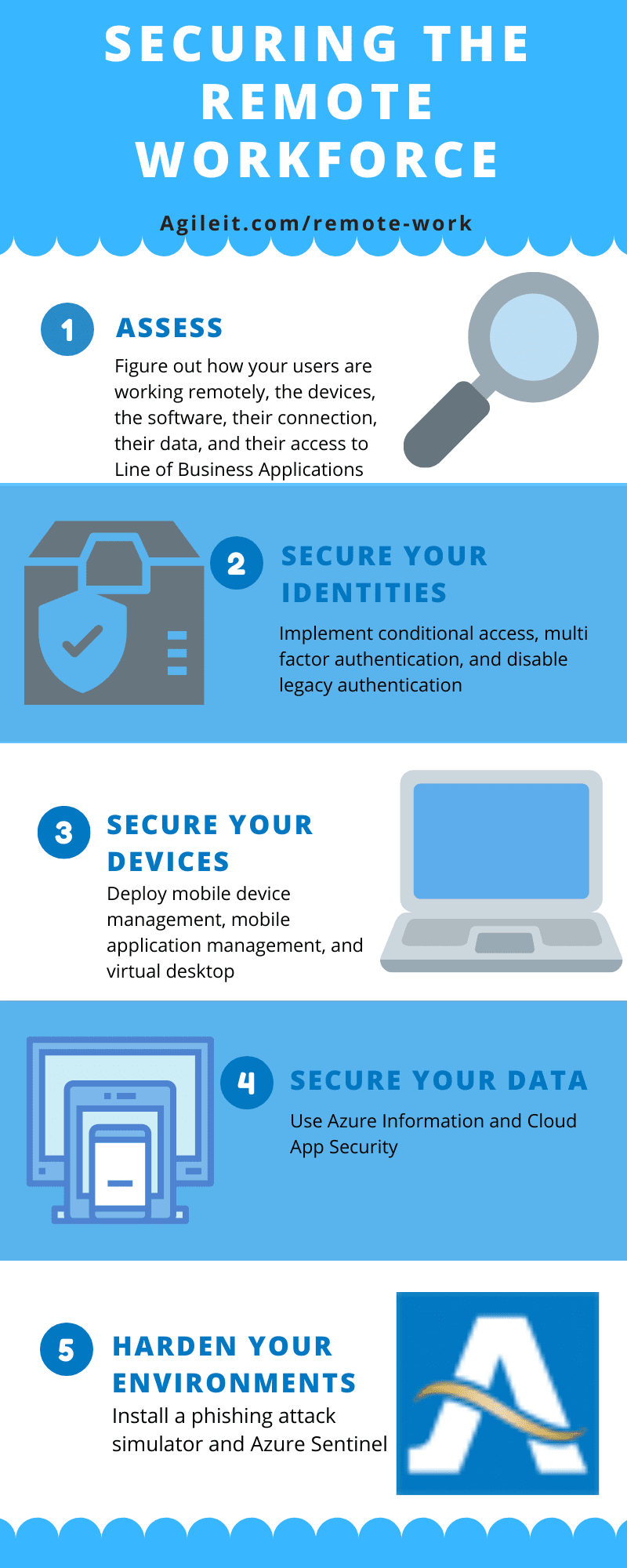
There are five steps in the process:
- Assess
- Secure your identities
- Secure your devices
- Then, secure your data
- Harden your environments
Step 1: Assess
The first step is to perform a baseline assessment of the various elements that are going into your employees’ remote work. This is a vital first step as it allows you to determine what policies and procedures your team will follow on the subsequent steps.
 Click to view infographic.
Click to view infographic.
This involves asking a series of questions to determine what practices they’re currently following:
How Are Your Users Working Remotely?
Are they all set up in home offices? Do their home offices have the necessary specifications? It’s crucial to understand the type of software each of your team members is planning to use as well as how they’re working. What specific projects are they working on? This will define what security measures to stay focused on.
What Devices Are They Using?
Is your remote workforce taking company-owned devices home, or is it a Bring Your Own Device (BYOD)-style set up? It’s a harder to maintain security for personal devices, however that doesn’t mean it’s impossible to secure these, but it may involve more work for your IT staff. It can also lead to issues if your team members experience IT or security issues down the road. Without a uniform set of equipment that everyone works from, it can lead to complications for your IT team in managing disruptions. You can manage either approach effectively, but they’ll have slightly different steps involved and you’ll need to understand what you’re dealing with before enacting other security measures.
What Software Are They Using?
Is everyone on the team using the same collaborative software? If they are, you can roll out the same educational and tutorial tools for your entire team. This also makes it much easier for your IT support staff - they’ll know what type of questions to expect and will be able to handle issues much quicker.
If not, why are they using different platforms? Having different team members using different types of software can represent more than a security threat - it can also lead to a lack of organization and added confusion when managing files. No matter what the case may be, it’s important to establish an understanding of what every team member is using.
How Do They Connect?
Does everyone on your team have a reliable, password-protected internet connection? What type of connection are they using? Make sure your team understands how to troubleshoot connectivity issues, has a decent connection, and knows who to contact if they run into problems. Since home WiFi networks can introduce a whole host of security concerns, be ready to advise your team on proper connection security.
Do They Manage Sensitive or Protected Data?
Managing sensitive or protected data makes following the proper cybersecurity protocols even more important. You’ll need to equip these team members with additional security measures ranging from data loss protection tools, to virtual machines to prevent the egress of data.
Do They Need Access to Specialized Tools or Line of Business Applications?
If there are any special programs or systems an employee will need to use remotely, you’ll need to ensure they have the right security measures in place.
Each of the above questions will impact how your team approaches remote security. If you have a team that collaborates using Office 365, you may also want to check out your Secure Score. This will give you actionable guidance you can use to solidify up your team’s security.
Step 2: Secure Your Identities
It’s also critical to secure your remote workforce member’s identities as you move to a remote posture. Implementing conditional access alongside multifactor authentication are two time-tested security measures that used together can stop 99% of hackers. Using hacker-detecting features such as impossible travel or seeing if a new device signed in with your credentials can also assist. These will let you know when a hacker has likely infiltrated your system using one of your employees’ information.
There are other measures you can take as well such as disabling legacy authentication that leads to breaches. Security provisions such as Just Enough Access and Just In Time make sure you grant access only to those who need it, limiting the number of people who can access your system.
Step 3: Secure Your Devices
The next step involves securing each team members’ device. The approach your organization takes here will vary based on a variety of factors. The method of security you embark on will depend on who owns your employee’s device and what type of device it is. Generally, there are three approaches you can take:
- Mobile device management. You can use this approach if your team members are using devices owned by the company.
- Mobile application management. This approach works if it’s a BYOD arrangement.
- Virtual desktop. Windows Virtual Desktop provides you with the capability to add multifactor authentication as well as conditional access policies to apply to your Azure Conditional Access portal. This allows you to secure, control, and limit access only to the appropriate parties.
If your team members are using your company-owned devices, it’s critical that you regularly check for updates to their anti-virus software. When your team is remote and they take company-owned devices home, inevitably at some point they’ll use it for personal reasons. This increases the risk of a potential malware attack.
Step 4: Secure Your Data
Losing data can be one of the most devastating and humbling experiences an organization can go through. A significant loss of data has the ability to set your team back in a major way. It can lead to loss of client trust, a decline in productivity, and if it’s serious enough, an impact on your bottom line. There are a number of measures you should take - and some you should be cautious when enacting - to prevent the loss of data.
It’s natural to want to adopt a data loss protection plan, but exercise caution when doing this for your remote team. It’s easy to implement protocols that are too rigid and aggressive. This could end up locking them out of the projects they’re working on. This is especially true if they’re using their own devices.
With Azure Information Protection, you can control who has access to your information. You can limit access to a select group. With Cloud App Security, you can protect your data even outside the environment. The protection can extend to your data in other systems or platforms such as Google Suite, DropBox, or Salesforce. You can even implement policies that allow you to prohibit screenshotting, copying and pasting, and other forms of data exfiltration on your employee’s devices - whether they’re employee or company-owned.
Step 5: Harden Your Environments

The following step represents the next level of security - putting policies in place to harden your systems from the threat of attacks. You can install a phishing attack simulator that can help prepare and protect your team members from a phishing attack. Incorporate a security information and event management tool such as Azure Sentinel to provide your team the ability to investigate threats and engage in forensic reporting.
You can also give your team the ability to learn about best practices for good cybersecurity hygiene. The key is to always focus on making incremental improvements to your team’s security, staying apprised of the most up to date patches and security requirements while keeping an eye out for emerging cyber threats.
Learn More About a Secure Remote Workforce
In summary, following the best practices outlined above can help you build a better, smarter, more secure remote workforce. Your employees shouldn’t expect to lose any productivity or connectivity when they work remotely. They should function identically to how they would in your traditional office environment. The same goes for their cybersecurity. With the right training and the right tools, there’s no reason they can’t be as secure in their home office as they are with your company.
To get the most out of the tools outlined above, it helps to partner with a trusted provider of managed IT services. Agile IT has been cloud-focused for 14 years and has a variety of services to increase the productivity, security, and compliance of your remote work environment. To find out how we can help, contact us today.





