Internet of Things (IoT) in the Workplace (Video)
Explore the transformative role of IoT in modern workplaces. Watch our video to understand the impact and benefits of IoT integration
Tech Talks are a weekly opportunity to learn how to do more with your cloud software and services. Each week, we feature a short talk from a subject matter expert, followed by a community driven Q&A where Agile IT customers can ask engineers any of their most pressing questions. This is a free service for our managed service clients. July 5th’sTech Talk was with John Gilham, CTO of Agile IT, who discussed how the Internet of Things (IoT) fits within a modern workplace.
What is IoT?
IoT is short for Internet of Things, the interconnection of computing devices embedded in everyday objects allowing them to send and receive data. The definitionof IoT has evolved due to the convergence of multiple technologies including:
- Real time analytics
- Machine learning
- Commodity sensors
- Embedded systems
The concept of a network of smart devices was discussed as early as 1982 with a modified coke machine at Carnegie Mellon University becoming the first internet connected appliance, able to report if inventory and whether newly loading drinks were cold.
Where is IoT being used?
Consumer applications
A growing portion of IoT devices are crated for consumer use, including connected vehicles, home automation / smart home, wearables, connecte health, and applicances with emote monitoring capabilities
Enterprise Applications
The term enterprise IoT refers to devices used in business and corporate settings. By 2019, it is estimated that EIoT will account for 9.1 billion devices.
Infrastructure Applications
Monitoring and controlling operations of sustainable infrastructure urban and rural infrastructure such as bridges, railways, and windfarms is a key application of the IoT. This IoT infrastructure can be used for monitoring events and changes in structural condition that compromise safety and increase risk.
Types of IoT
Integration of existing IoT connected services
Off the shelf IoT devices enable business to quickly take advantage of IoT benefits (such as Alexa controlling the TV, projectors, lights, etc.)
Tying cameras to badge based access controls
In retail, tying cameras to POS systems
No need to buy or build services, as the service are already built
IoT for custom business enablement
- Compliance Monitoring
- Preventative Maintenance
- Remote diagnostics
- Asset Tracking
- Automatic Fulfillment
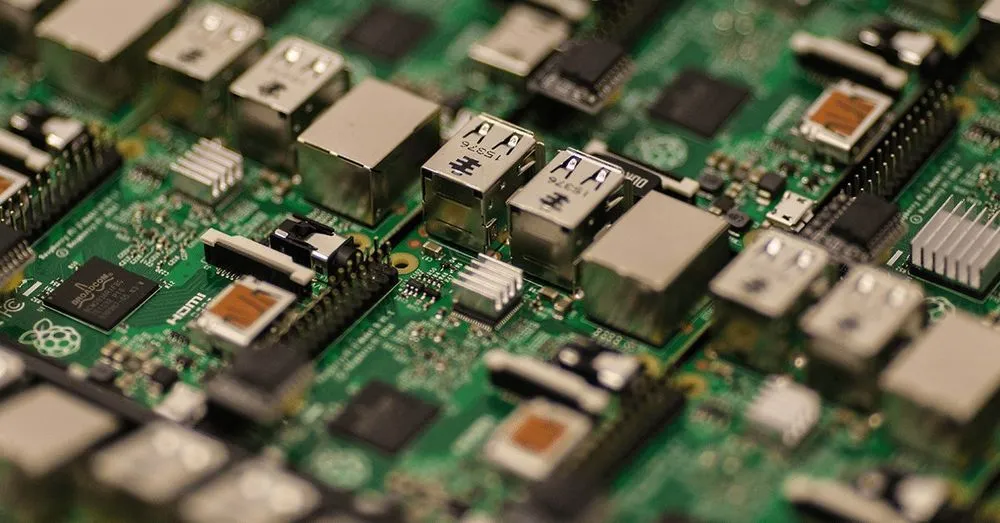
Windows 10 IoT Devices IoT Azure Edge certified devices
IoT Architecture
Cloud Processing
Pros:
- Develop and deploy applications quickly
- Scale as needed while validating new product ideas
- No longer neededing to maintain your own data centers
Cons:
- Unpredicitable response time from Cloud Servers to End Points
- Unreliable internet connections can bring down services
- Excessive data can overburden infrastructure
- Difficulties in ccaling due to ever increasing number of servers and actuators
Fog Computing (Closer to the ground)
An architecture that uses edge devices to carry out a major portion of the processing, storage and communication, it uses Traditional Cloud IOT Devices but using local resources instead of centralized processing.
AI Based (Drones, autonomous vehicles)
The drawbacks of cloud-centric design makes is unsuitable for mission critical industrial or healthcare applications
Agile IT’s Office IoT Services
John discussed the IoT sandbox we have in our offices at Agile IT, including:
- Building Automation
- Alarm
- Cameras
- Access Control
- Blinds
- Centralized HDMI wiring
- Media Player for HDMI and Overhead Speakers
- Infared Blaster to control IR devices
- Overhead Speakers
Examples of How Agile IT Connects IoT Services into Business Scenarios
- Secure Data Center Monitoring
- Monitoring local IT resources at customer locations requiring enhanced security and Personally Identifiable Information (PII) protection
- Monitoring server and network components
- (Temperature, Storage, Network, processing metrics)
- Processing and storage analytics to identify trends and capacity analysis
- Easy Closing Automations
- Swipe badge to arm alarm
- Music Stops, over head announcement on speakers that alrm is arming
- TVs shut down
- Lights turn off
- Blinds come down in all offices
- HVAC set to away mode
- Visitor Notification
- Doorbell run on alarm system
- Announcement made on overhead speakers
- Popups on receptionist PCs
- Anywhere Control of Security
- Lockdown
- Camera Control
- Access Control Logging
- Mail to Accounting
- All mail scanned All bills forwarded to bill.com which uses OCR to code them to our vendors
- This is automatically synched to our account service
- Checks automatically deposited
- Interviewing
- Smartphone of web app allows video interviewing of applicants on their own schedule
- Integrated with our Applicant Tracking System so interview synched when completed.
Evolving use cases of IoT in business
- Data center monitoring management and automation
- Supply chain and inventory management
- Surveillance and security monitoring
- Contextual product features
- Building and facilities management
- Asset management
- Fleet management, telematics
- Healthcare
- Retail
- Insurance





