CISA Security Recommendations for Office 365
The Department of Homeland Securitys Cybersecurity and Infrastructure Security Agency CISA has released an alert as an update to its May 2019 Analy...

The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) has released an alert as an update to its May 2019 Analysis report titled, “AR19-133A: Microsoft Office 365 Security Observations.” This alert outlines recommendations on security and threat mitigation efforts that organizations can implement for Microsoft Office 365.
There are eight security measures CISA recommends. Indeed, implementing these measures will help keep your systems and applications more secure during Office 365 migration. Below is a description and analysis of each recommendation you can use for your organization:
Multi-Factor Authentication for Administrators
If you’re a GCC High client, this should be your first step before you migrate to assure you’re operating in a secure environment. Under Azure Active Directory, no user has as many capabilities as the Global Administrators. Thinking of it in terms of an on-premises AD setup, they have the same access abilities as a Domain Administrator. Global Administrators’ are the first accounts set up to oversee the rest of the migration. The issue with this is that multi-factor authentication is not the default setting for administrator accounts. That means the organization must take the effort to enable this protocol. Without performing this action, this leaves a vulnerability where a malicious actor who exists in the on-premise environment can compromise any cloud-based accounts and maintain a presence there as more users migrate to Office 365.
Use Role-Based Access Control (RBAC) to Assign Administrator Roles
As noted above, the Global Administrator has more privileges than any user within your environment. If compromised, it could prove catastrophic to the organization’s data. It immediately exposes the entire organization’s systems and applications to an attack. That’s why it makes sense to use other roles within Azure AD that have administrator privileges. Thus, you can limit the number of privileges each administrator has to the roles that pertain to their job and nothing more. No one administrator will have permissions that aren’t required for their role.
For more on how to enable Just Enough Access and Just In Time Access, check out this podcast episode where AgileIT’s CEO, Conrad Argamont, touches on Identity Privilege Management.
Enable the Unified Audit Log
Unified Audit Log (UAL) is Office 365’s logging capability. With events from SharePoint Online, Azure AD, OneDrive, Exchange Online, and Microsoft Teams, PowerBI, and various other Office 365 applications, it gives you a comprehensive ability to run queries across your organization’s Office 365 landscape. To do so, an administrator must first enable this in the Security and Compliance Center. Once it’s enabled, UAL will then grant your administrators the ability to determine when an application or system has been compromised — or if there’s been activity going against company protocol. UAL essentially provides you with enhanced visibility into any threats.
Encourage and Enable Multi-Factor Authentication for Every User
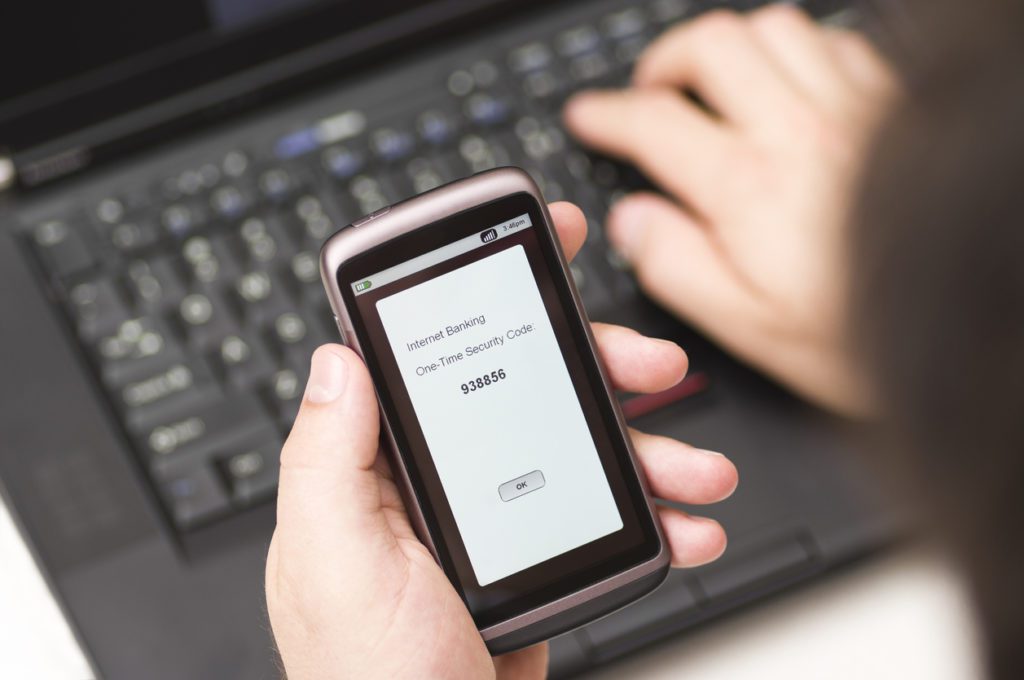
Multi-factor authentication provides an added level of integrity for every user’s log-in. This is true no matter what kind of permission they have across your Office 365 platform. Even if they don’t have administrator privileges, all users still have access to information that could harm the organization. Normal accounts can also receive phishing emails from malicious actors that lead to attacks of any apps the affected user can access. Multi-factor authentication is the least every member of your organization can do to secure themselves while using the system. Make it a standard policy across all departments.
Disable Legacy Protocol Authentication
Many of the legacy protocols for Exchange Online — the application that provides Office 365 with email services — do not support multi-factor authentication. Three of these protocols include Post Office Protocol (POP3), Simple Mail Transport Protocol (SMTP), and Internet Message Access Protocol (IMAP). These protocols are relics of a bygone era and are used with older email clients that aren’t compatible with modern authentication features. That’s why you should disable these protocols (unless your organization views the use of these older email clients as a necessity).
If you opt for this, be warned — email addresses will be accessible with only a user name and password, which can represent a security liability. One possible workaround here is to keep track of and inventory these users, only granting access to legacy protocols to them. That’s where Azure AD’s Conditional Access policies will be useful. Indeed, they can prevent users who don’t need the legacy access protocols from using them.
Enable Suspicious Activity Alerts
Being able to respond quickly to suspicious activity is integral to your organization’s ability to stay secure. That’s why you should enable suspicious activity alerts. This logs any out of place activity within Office 365, letting administrators know that something is amiss. When administrators receive this notification, it cuts down on the time it would have taken them to identify the issue and respond. CISA’s minimum recommendation is to enable alerts for suspicious location logins or if a user sends too many emails.
Use Microsoft Secure Score
Despite taking all necessary precautions, how can you be sure your organization is as secure as possible from an Office 365 service perspective? By using Microsoft Secure Score. This tool, built into Office 365, will analyze your organization’s current security levels while offering recommendations on how to improve. While the recommendations are not comprehensive of all security measures you can take, it does making tracking security requirements in Office 365 much easier. It provides you with a central hub to track any security and compliance changes Microsoft implements. You’ll have an easier time staying up to date on any changing requirements.
Integrate Logs With Existing SIEM Tool
Lastly, CISA recommends using an SIEM tool to manage your logs. Microsoft offers a solution for this: Azure Sentinel, their SIEM system. It involves a simple process to integrate your Office 365 logs. This helps you sync up Office 365 and your organization’s environment, ensuring you can capture any activity.
The Bottom Line on Secure Office 365 Migration
Following the above recommendations gives you the best chance possible at a completely secure Office 365 migration. These best practices ensure you can mitigate risks while keeping your entire environment — including Office 365 — safe. Indeed, it protects all company systems and data from being compromised. Agile IT already uses these mitigations are the baseline for all of our security onboarding projects. To find out if your remote workforce is secure, and help get there faster, contact us today.





